Automotive Security
History
Guide
Your Car Key Is a 100-Year Arms Race
From a simple blade of brass that barely kept honest people out, to an encrypted digital handshake that happens in nanoseconds — here's how engineers and thieves have been going back and forth since the Model T.
By The NPZ Team
·
Automotive Security
·
March 2026
·
12 min read
There's a key on your keychain right now that contains more computing power than the Apollo 11 guidance computer. It communicates with your car via encrypted radio signals, knows exactly how far away it is in three-dimensional space, and can be deactivated remotely from across the country. It's also — if your car is older than about 2010 — probably sitting on your kitchen counter broadcasting its location to any thief within 30 feet with a $30 signal amplifier from Amazon. The history of the car key is a story of brilliant engineering, immediate criminal exploitation, and the next round of even more brilliant engineering. Repeat forever.
We're going to walk through every major chapter, explain how each system actually works, and tell you exactly which vulnerabilities your car probably has right now.
In the earliest days of motoring, the car key didn't start the car — it unlocked the ignition switch so you could crank the engine by hand. The lock was essentially a formality. It was there to signal that this was a serious machine that required authorization, not because the lock itself was any great security barrier. Any reasonably determined person with a piece of wire and five minutes could bypass it.
Everything changed in 1949 when Chrysler introduced what we'd recognize as the modern ignition key: a single key that simultaneously completed the electrical circuit and engaged the starter motor. No more hand cranking. One turn, engine starts. The flat, single-sided blade became the universal standard almost immediately — elegant, simple, cheap to produce. It was also, by every modern measure, barely a security device at all. The key only needed to fit the lock in one orientation, which meant key blanks were plentiful and locksmiths could cut a copy in minutes. Hotwiring — bypassing the ignition cylinder entirely by connecting the starter wire directly to the battery — was well within the skill set of any teenager who'd read a basic automotive manual.
⚡ The Hotwiring Reality Check
Hotwiring a pre-1990s car is genuinely as simple as it looks in movies — find the ignition wires under the steering column, strip them, connect battery to ignition, touch starter wire briefly. On most classic cars it takes under two minutes. This is why classic car theft rates were historically very high and why any pre-transponder vehicle should have a supplemental mechanical kill switch or steering wheel lock if it's parked outside regularly.
In 1965, Ford introduced the double-sided key — the same cut pattern on both the top and bottom of the blade, so drivers no longer had to fumble in the dark to figure out which way the key went. It was a genuine quality-of-life improvement. As a security advancement, it was essentially worthless. Having twice as many possible orientations doesn't change the fact that the underlying cut pattern is still a simple warded mechanism that any halfway competent locksmith could defeat in seconds.
What the double-sided key did accomplish was starting to make key cutting slightly more complex — you now needed to cut both sides correctly. But hotwiring remained trivially easy, lock-picking was straightforward, and "jiggle keys" — blanks cut to approximate patterns that could open worn ignition cylinders through vibration — were a real thing that real thieves actually used. The double-sided era is best understood as the automotive industry telling itself it had solved the security problem while actually solving the fumbling-in-the-dark problem.
By the mid-1980s, car theft in the United States had reached crisis levels. Automakers needed a solution that didn't require redesigning the entire ignition system from scratch. GM's engineers came up with something beautifully simple: a small black pellet embedded in the key blade of the 1986 Corvette. They called it the Vehicle Anti-Theft System, or VATS.
Here's the important thing that most people get wrong about VATS: it was not a computer chip. It was a resistor — a passive electrical component with a specific resistance value. The ignition cylinder had electrical contacts that read the resistance of the pellet. If the resistance didn't match one of 15 possible values encoded in the car's security module, the module would disable the starter and the fuel injection system for several minutes. Hotwire the ignition? Doesn't matter — the engine won't stay running without the right resistance value in the key.
⚙️ How VATS Actually Worked
1
Key inserted into ignition cylinder — two electrical contacts in the cylinder touch the resistor pellet embedded in the key blade.2
The VATS security module reads the electrical resistance value of the pellet (one of 15 possible values, from about 400Ω to 11,800Ω).3
If the resistance matches the programmed value, the module enables the starter relay and fuel injectors. Engine starts normally.4
If the resistance is wrong (or the key has no pellet), the module disables the starter and fuel system for 2–4 minutes, resetting on each wrong attempt.
⚠️ The VATS Vulnerability
A determined thief with a multimeter could measure the resistance of a captured key or probe through the wiring to find the correct value — then hardwire a matching resistor directly into the system, permanently bypassing VATS. It wasn't trivial, but it was possible. For casual thieves, though, the 2-4 minute lockout was enough to make them move on. Crime prevention doesn't require perfection — it just requires being harder to steal than the car parked next to you.
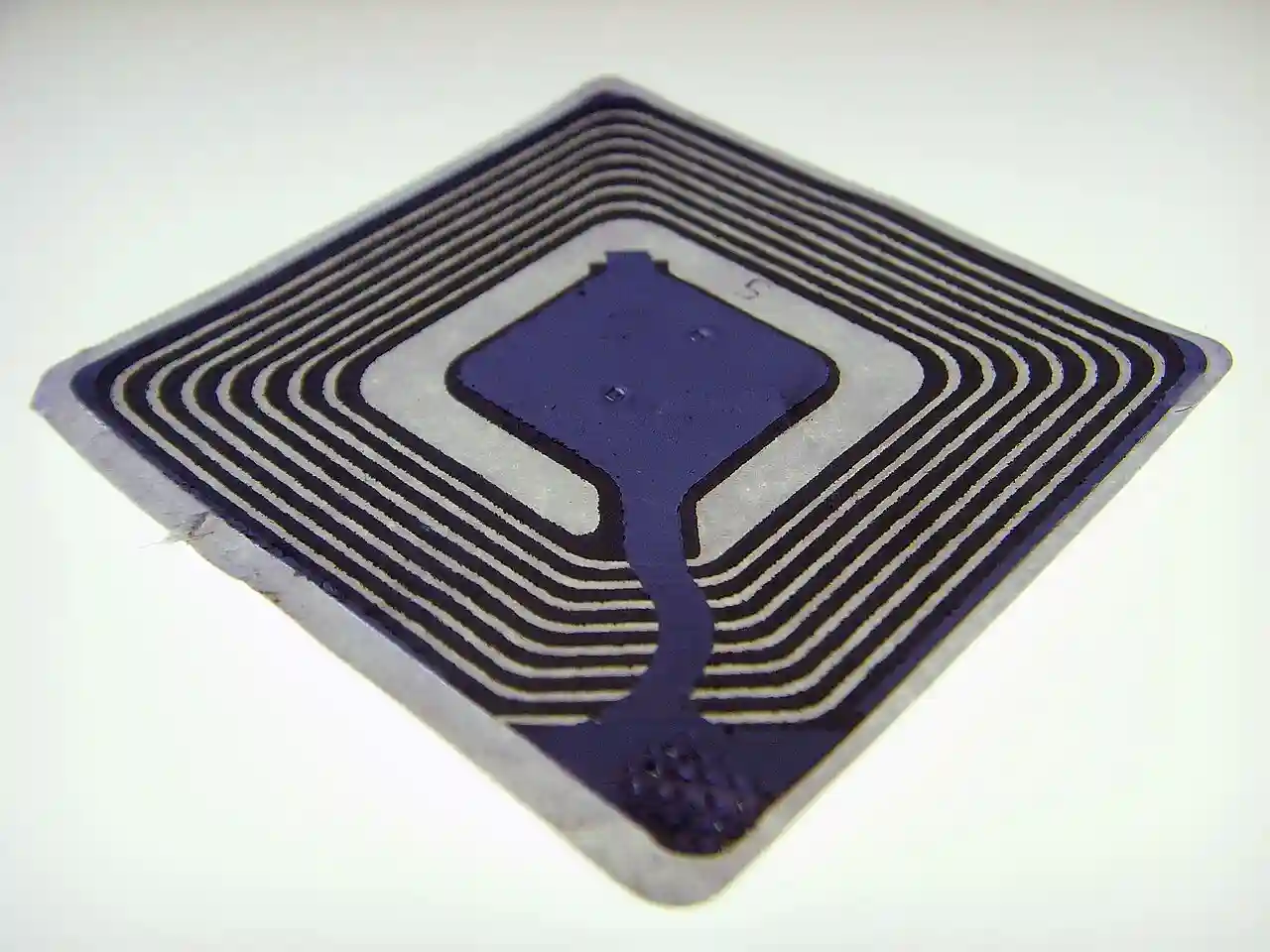
The transponder key was the first genuinely secure automotive security system. Instead of a passive resistor, the key's plastic head now contained an active RFID chip — a tiny computer that could receive power wirelessly and transmit a unique digital code. This wasn't just harder to bypass than VATS; it was a fundamentally different class of security problem.
⚙️ How Transponder Keys Work
1
An induction coil wound around the ignition cylinder generates a low-power electromagnetic field when the ignition is switched on.2
The RFID chip inside the key head harvests energy from this field — no battery needed. The chip "wakes up."3
The chip transmits its unique rolling digital code back to the car's ECU (Engine Control Unit) via radio frequency.4
The ECU compares the received code to its programmed value. Match = fuel delivery enabled, engine runs. No match = engine dies within seconds, even if the ignition cylinder is physically turned.
The transponder era effectively killed hotwiring as a viable theft method on modern vehicles. Even if a thief bypassed the ignition cylinder entirely, the engine would start briefly and then stall — the ECU refusing to supply fuel without the correct rolling code from the key. This is why hotwiring only works in movies and on cars built before the mid-1990s.
Crucially, the code was a rolling code — it changed with every use, using a cryptographic algorithm shared between key and car. Capturing the transmission didn't give you a reusable key; you'd have a code that had already been used and was now invalid. Professional "code grabbers" did exist and could perform more sophisticated attacks, but casual theft became essentially impossible on transponder-equipped vehicles.
🔍 The Locksport Angle
Transponder chips created a problem that's familiar to anyone in the lock world: the physical cylinder became irrelevant to the real security. A skilled lockpicker could open the ignition cylinder in seconds — but the engine still wouldn't run without the chip. Security had migrated from the mechanical to the electronic layer. The cylinder was now just a way to turn the switch. The real barrier was in the code.
While transponders handled the electronic security layer, the physical key blade was still the same toothed design it had been since the 1940s. High-end manufacturers — BMW, Mercedes, Audi — decided to address that separately. The laser-cut key, also called a sidewinder or internal-cut key, has a winding track milled down the center of the blade rather than teeth along the edge.
The differences from a security standpoint are significant. Standard toothed keys can be cut on a $500 machine and duplicated at any hardware store with a matching blank. Sidewinder keys require precision CNC milling equipment that costs tens of thousands of dollars — not something your local Walmart key kiosk is running. The internal track also engages the ignition wafers from the side rather than the top and bottom, creating tighter tolerances that make both lock-picking and jiggle-key attacks significantly harder.
Restricted keyways took this further — blanks for certain high-security keys are only available through authorized dealers, requiring proof of ownership to duplicate. This is the same concept as restricted keyways on residential locks like Medeco or Mul-T-Lock: key control as a security layer. Your locksmith can't cut a copy if they can't get the blank.

In 1998, Mercedes-Benz introduced "Keyless Go" — the physical act of inserting a key into an ignition slot disappeared for the first time in automotive history. You kept the fob in your pocket. You touched the door handle; the car unlocked. You pressed a button; the engine started. A computer handled everything in between.
Modern proximity fobs work through a constant, low-power two-way radio dialogue between car and key. The car continuously broadcasts a low-frequency (LF) challenge signal. When the fob enters range — typically 1–3 meters — it picks up the challenge, processes it, and transmits an encrypted response on a higher frequency (UHF). The car verifies the response, and access is granted. The whole exchange takes milliseconds.
This is enormously convenient. It also introduced the most significant automotive theft vulnerability since hotwiring.
The Relay Attack — The Thief's Cheat Code
Here's the problem: the fob never stops broadcasting. It's always listening and always ready to respond. It doesn't know or care whether the signal it's receiving is coming from your car three feet away or from a relay device pointed at your living room window from the sidewalk outside.
⚙️ How a Relay Attack Works
1
Thief #1 stands near your front door or window with a signal amplifier — a device that boosts and relays the car's LF challenge signal into your house, where your key fob is sitting on a table.2
Your fob, now receiving what it thinks is a nearby car signal, responds with its encrypted unlock code.3
Thief #2 stands next to your car with the matching relay receiver. Your car receives the fob's response, thinks you're standing outside, and unlocks.4
Thief #2 gets in and starts the engine. The car is gone in under 60 seconds. No forced entry. No broken glass. Your key never left the house.

⚠️ Is Your Car Vulnerable?
If your car has a push-button start and you've never heard of a relay attack, assume you're vulnerable. Most push-to-start vehicles made before 2022 without explicit UWB protection can be stolen this way. The relay equipment required costs around $30–$200 on the grey market and requires no technical skill to operate. Insurance companies in the UK now classify certain keyless-entry vehicles as higher theft risk for this reason.
✅ The Faraday Fix — Simple and Effective
A Faraday pouch is a small foil-lined bag that blocks all radio signals. Drop your proximity fob in one at night and the relay attack is physically impossible — there's no signal to amplify. They cost $10–$20 on Amazon. If you have a push-to-start car, this is the single highest-value security upgrade you can make for the price. Alternatively, a metal tin or even your microwave (don't run it) will work in a pinch. Some manufacturers now include motion sensors in fobs that put them to sleep when stationary — check if your car has this feature.
Advertisement · 728 × 90
Ultra-Wideband (UWB) technology is the current state of the art in automotive security, and it solves the relay attack problem in a genuinely elegant way. Instead of just exchanging encrypted codes, UWB measures the precise time of flight of the signal — the exact number of nanoseconds it takes for the radio wave to travel between the car and the key. Since radio waves travel at the speed of light, this gives the car an accurate distance measurement down to about 10 centimeters.
"A relay attack amplifies the signal but cannot compress time. If the key is 30 feet away, the time-of-flight says 30 feet — and the car stays locked."
— The principle that makes UWB relay-resistant
Apple, BMW, and several other manufacturers began deploying UWB in 2020–2022. Apple's U1 chip, found in iPhones since the iPhone 11, uses UWB for the "Precision Finding" feature in AirTags and enables Precision Car Key on compatible BMW and other vehicles. The car knows not just that the key is nearby but exactly how far away and in what direction. A relay device amplifying the signal from inside your house can't fake that the key is three feet from the door handle when it's actually 30 feet away — physics won't cooperate.
Digital Keys and Your Smartphone
The logical end point of this trajectory is no physical key at all. Digital key standards — built around NFC (for tap-to-unlock) and UWB (for proximity detection) — let your smartphone act as your car key. BMW, Hyundai, Kia, and others already support this. The Car Connectivity Consortium's Digital Key standard means your phone can start a supported car even if the phone's battery is dead, using a low-power NFC reserve mode.
This introduces new attack surfaces — your phone's security, the OEM's server infrastructure, the app itself — but also new capabilities: sharing temporary digital keys with a family member or valet, setting geographic restrictions on a shared key, or revoking access instantly from anywhere in the world. The credential is finally software, and software can be managed in ways a brass key never could.
⚡ The OBD Port Threat — Modern Professional Theft
The other major current threat isn't signal-based at all. Professional theft rings now use OBD (On-Board Diagnostics) port programming to clone key fobs. Gain physical access to the car — often by breaking a window — plug a programmer into the OBD port under the dashboard, and use it to program a blank fob to the car's ECU in minutes. Drive away with a factory-fresh key. Countermeasures: an OBD port lock (a physical block that prevents access to the port), or a GPS tracker. Neither is perfect, but the OBD lock buys time.
Key Evolution at a Glance
The Bottom Line
The Pattern Never Changes — Only the Battlefield
Every generation of automotive security solved the attack that came before it and created the conditions for the next one. The ignition lock stopped casual access. Hotwiring defeated that. Transponders killed hotwiring. OBD port cloners defeated transponders. Proximity fobs eliminated the ignition key. Relay attacks defeated proximity fobs. UWB defeated relay attacks. Something will eventually defeat UWB.
The lesson isn't to give up — it's to understand where your car sits on this timeline and act accordingly. If you have a push-to-start car and no Faraday pouch, you have a meaningful vulnerability that costs $15 to fix. If you have an older car without a transponder, a secondary mechanical immobilizer or hidden kill switch is worth the investment. If you're buying a new car, UWB support is worth checking for.
The same principle applies to every lock on this site: no security system is permanent. The goal is to stay ahead of the casual thief and make the professional thief's job more expensive than your car is worth. At a certain point, they'll find a softer target. That's always been the game, from Bramah's challenge lock to your key fob. Make their job harder than it's worth.