Deep Dive
Complete Guide
History + Mechanics
The Lock That Doesn't Play by the Rules
No springs. No shear line. No bump key. The disc detainer lock operates on entirely different physics from every other lock you've ever owned — and it's been doing it since 1907. Here's the full story: where it came from, exactly how it works, how you'd pick one, and which ones are actually worth buying.
By the NPZ Team
·
Guides · Deep Cuts
·
March 2026
·
25 Min Read
In 1907, a Finnish mechanic named Emil Henriksson was repairing a cash register in Helsinki when he noticed something. The machine's internal counting discs — small rotating cylinders that clicked through positions as numbers were tallied — were doing something interesting. Each disc could sit at a precise rotational angle, stable and independent of the others. If you controlled those angles, you controlled the machine.
Most people would have fixed the register and gone home. Henriksson saw a lock. Not a metaphor — an actual, physical lock built on the same principle. Two years later, he had one. And over a century later, the best version of his idea is still the mechanical security benchmark for critical infrastructure, telecommunications networks, maritime shipping, and the most obsessive corner of the locksport community.
The reason it's survived a century of being attacked, analyzed, copied, and improved is simple: it works on fundamentally different physics from every other common lock. No springs means no bump attack. No shear line means traditional picking tools don't apply. No exposed driver pins means a whole category of vulnerabilities simply doesn't exist. This guide covers all of it — the history, the mechanics, the security features, the picking theory, and the tools. And at the end, we'll tell you which ones to actually buy.
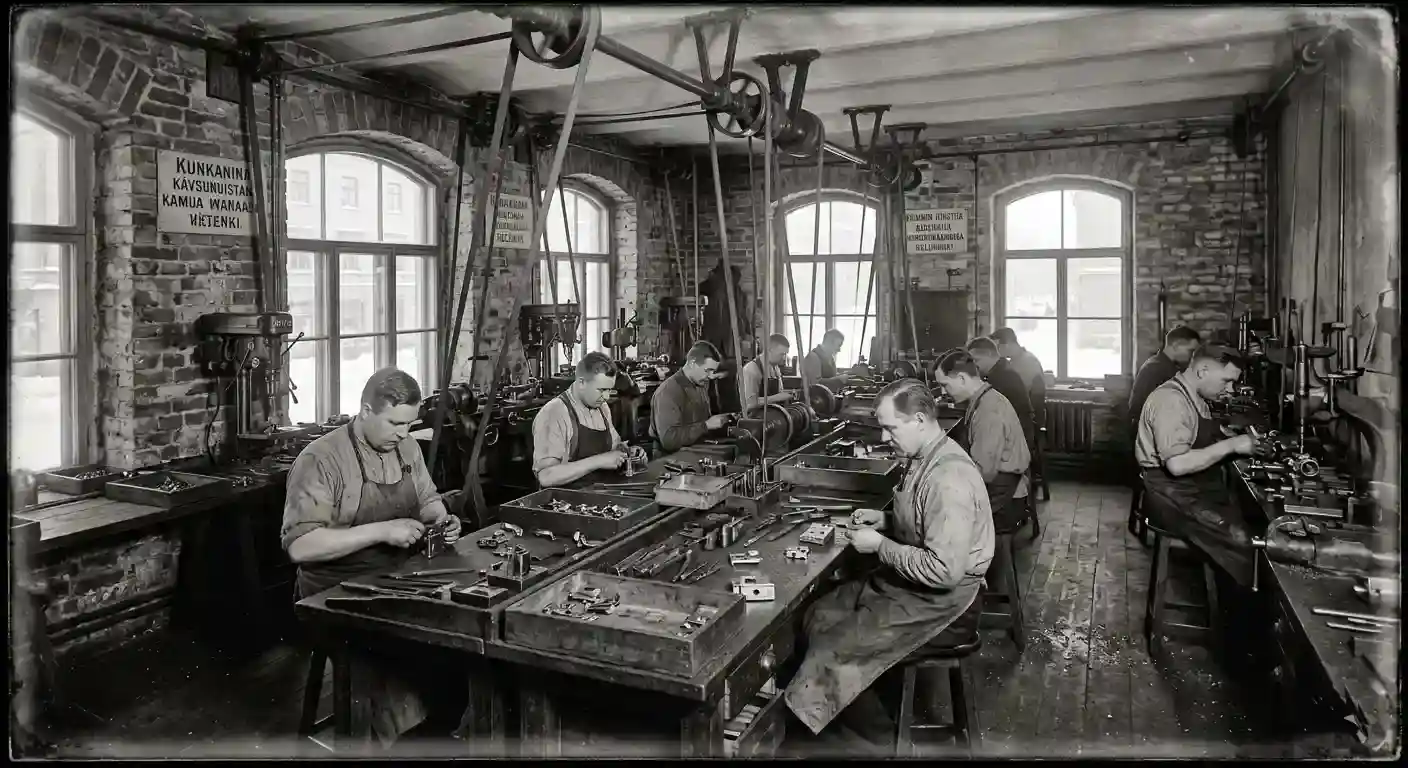
The disc detainer lock has an unusually specific origin story — unusual because it's actually true and documented, not the kind of fuzzy mythology most security inventions get buried in. Emil Henriksson was not a locksmith. He was an office machinery mechanic. He was not trying to invent a lock. He was trying to fix a cash register.
What he recognized in 1907 was that the rotating counting discs inside that register obeyed a principle with enormous potential: position determines state. Control the rotation of each disc independently, and you control whether the machine opens or stays locked. The insight wasn't about locks — it was about rotational geometry. Locks just happened to be the most obvious application.
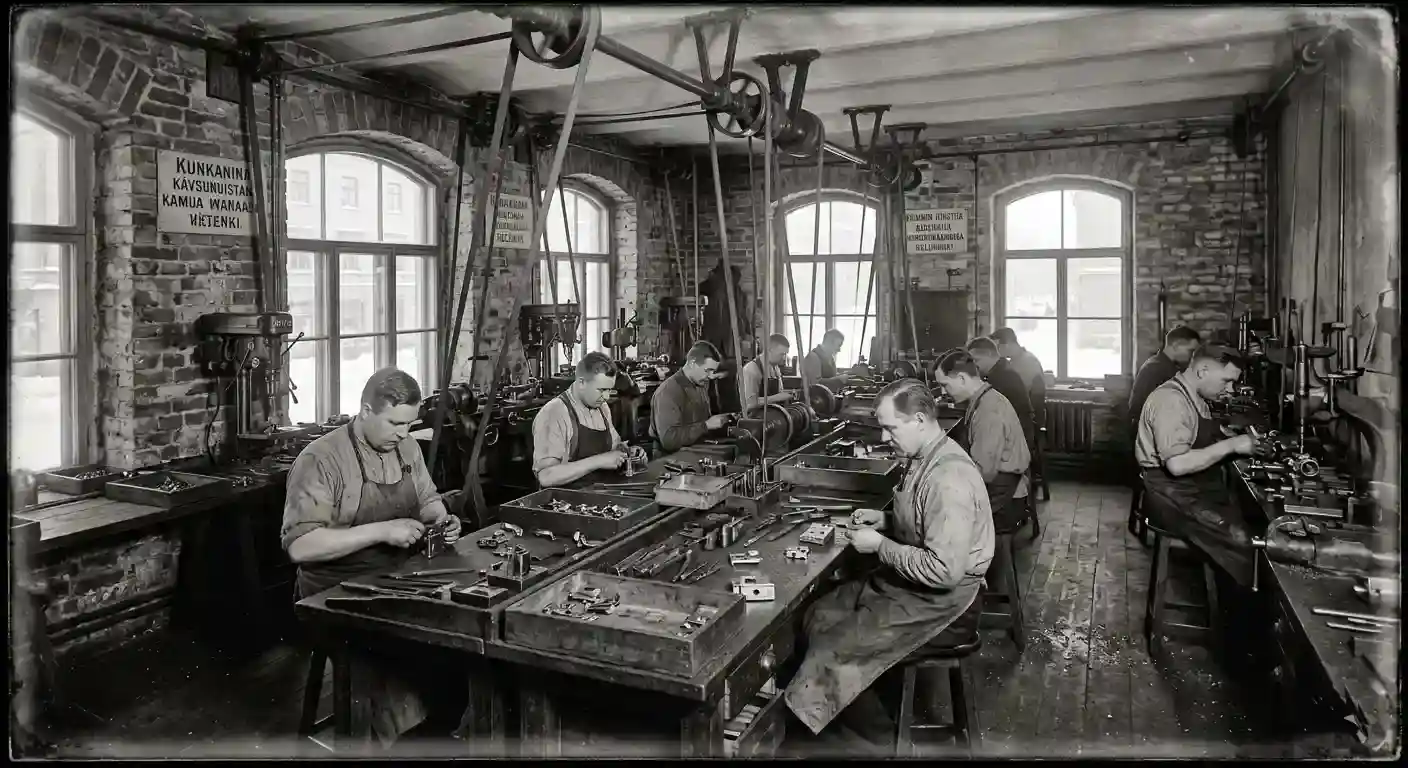
The first commercial locks reached the market in 1909. By 1918 — in the chaos of post-WWI reconstruction and the new demands of industrial infrastructure — a dedicated manufacturing company, AB Lasfabriken, was formally founded in Helsinki to scale production. The mechanism was patented in 1919 under the name "Henriksson's Patent Lock," and the ABLOY trademark was registered the same year, derived from the company's Finnish name, Ab Lukko Oy.
⚡ Finnish National Treasure
The Foundation for Finnish Inventions has listed the Abloy disc detainer lock as the most significant invention in Finnish history. That puts it ahead of the sauna thermometer, the Linux kernel, and SMS texting. Finland takes its locks seriously.
The 20th century brought a series of corporate integrations that gradually turned a small Helsinki company into a global security conglomerate. Acquired by Kone & Siltarakennus in 1923, absorbed into the Wärtsilä Group in 1936, the company's lock division was always the core, always the product that justified the rest. The landmark moment came in 1994 when Abloy merged with the Swedish firm ASSA to form ASSA ABLOY Group — now the world's largest lock manufacturer, present in virtually every country, with disc detainer technology at the heart of its high-security product lines.
1907
The Epiphany
Henriksson sees the cash register discs
While repairing office machinery in Helsinki, Emil Henriksson recognizes the security potential of rotational disc alignment. The "rotate-and-align" principle is born.
1909
Commercial Launch
First disc detainer locks reach market
Two years after the initial concept, working locks are sold commercially in Helsinki — before the patent is even filed.
1919
Patent + Brand
ABLOY trademark registered
The "Henriksson's Patent Lock" is formally protected. The ABLOY brand emerges from Ab Lukko Oy — the name that will define the technology category for a century.
1968
The Modern Factory
Joensuu R&D center opens
A dedicated research and production facility in Joensuu, Finland becomes the global epicenter for disc detainer innovation — a role it still holds today.
1978
Electronic Pioneer
First electric disc detainer lock
Installed for the Bank of Finland — decades before electromechanical locks became mainstream. The foundation for CLIQ technology is laid.
1994
Global Consolidation
ASSA ABLOY merger
The combination of Swedish ASSA and Finnish ABLOY creates the world's dominant lock group. Disc detainer technology goes fully global.
2001
The Benchmark
Abloy Protec launches
Eleven discs, nearly 2 billion combinations, and the Disc Blocking System. Protec sets the standard that all other mechanical locks are measured against.
2012
Current Standard
Abloy Protec2 replaces Protec
An interactive moving element in the key defeats 3D-printed duplicates. Patent protection extended to 2031. The current high-water mark for mechanical security.
To understand why disc detainer locks are so secure, you first need to understand what almost every other lock is doing — and what it isn't. A standard pin tumbler lock (your deadbolt, most padlocks, basically everything Kwikset or Schlage makes) works on a vertical principle. Pins are pushed up by springs. Your key pushes specific pins to a precise height so they align at a "shear line." When all pins hit that line simultaneously, the plug rotates. Simple, elegant, and in use since the 1840s.
The problem is that the springs are both the feature and the vulnerability. They give pins a default state — which means you can feel them when picking. They respond to kinetic energy — which is exactly what a bump key exploits. And in cold, wet, or corrosive environments, springs are the first thing to fail.
Disc detainer locks throw all of that out.
The Core Principle: Rotational Alignment

Inside a disc detainer cylinder, instead of vertical pins, there is a stack of circular metal discs — anywhere from 5 to 11, depending on the lock's security tier. Each disc can rotate independently around a central keyway. Each disc has a precisely machined notch — called a true gate — cut into its outer edge.
Running along the side of the disc stack is the sidebar: a longitudinal bar that sits in a groove cut into the cylinder housing. In the locked position, the discs are rotated to random positions, so their outer edges block the sidebar from retracting. The sidebar physically prevents the plug from turning.
When you insert the correct key, the angled bitting cuts on the key blade engage the internal profiles of each disc and rotate them to specific angles. Turn the key 90 degrees and — if it's the right key — every single disc's true gate is now aligned at the same position. The sidebar, no longer blocked, drops into that channel of aligned gates and retracts from the housing. The plug turns. The lock opens.
🔄 The Opening Sequence — Step by Step
1
Key insertion: The key passes through the disc stack via the central keyway. At this point, nothing moves — the key is just seated.
2
Rotation begins: As the key is turned, the angled bitting cuts press against each disc's internal profile, rotating each disc to its unique required angle.
3
Gates align: On the correct key, the final 90-degree turn results in every disc's true gate aligning in a continuous channel along the sidebar position.
4
Sidebar retracts: With nothing blocking it, the sidebar drops inward, freeing the cylinder plug to continue rotating and actuating the bolt or cam.
5
Return: When the key is turned back and removed, the mechanical action of the key itself scrambles the discs back to their locked positions. No springs required.
That last point — no springs required — is the fundamental difference. In a pin tumbler lock, springs are what reset the pins when the key leaves. In a disc detainer, the key's reverse rotation is the reset mechanism. The discs are driven by the key on both insertion and removal. This is why disc detainer locks work flawlessly at -40°C, underwater, in saltwater spray environments, and after years of outdoor exposure. There are no springs to freeze, corrode, or weaken.
The Math: How Many Combinations?
The theoretical number of possible key combinations in a disc detainer lock is straightforward to calculate: it's the number of disc positions raised to the power of the number of discs. The Abloy Classic uses 6 distinct rotational positions per disc (in 18-degree increments from 0° to 90°), with up to 11 discs — giving a theoretical maximum of over 36 million combinations. In practice, the number of valid working keys is lower due to mechanical constraints: some discs serve as steering elements, and certain bitting patterns are excluded to prevent "parasitic drag" — the unintentional co-rotation of adjacent discs. The valid differ count for the Abloy Classic is approximately 9.7 million.
The Abloy Protec2 uses 11 discs with significantly more rotational positions, reaching 1.9 billion valid combinations. For context: if you tried one key combination per second, it would take over 60 years to exhaust them all by brute force.
⚡ Inside the Disc Stack: Key Components
- Detainer Discs: Brass or hardened steel. The primary "tumblers." In high-security models, the first disc is free-floating and hardened specifically to resist drilling.
- Washers & Spacers: Thin rings between each disc that prevent the rotation of one disc from dragging its neighbor — the "parasitic drag" problem.
- Sidebar: Budget locks use a round sidebar. High-security Abloy models use an L-shaped sidebar since the 1980s, increasing gate engagement area and making it dramatically harder to drill out.
- Disc Controller (DC): Found in Abloy Disklock Pro and Protec models. A ball bearing that must seat in a specific dimple on the key before the plug can rotate, protecting internal components from partial-insertion damage.
A disc detainer lock's security isn't just a result of the rotational principle — it's the result of specific engineering features layered on top of that principle. Each one addresses a different attack vector. Here's what's actually between a would-be intruder and a high-quality disc detainer cylinder.
False Gates: The Trap
This is the feature that makes even experienced pickers sweat. In addition to the true gate, high-security discs have false gates — notches machined into the disc's outer edge that are shallower than the true gate. When a picker applies tension and probes the discs, the sidebar can partially drop into a false gate. It feels like a set disc. It sounds like a set disc. The tactile feedback is nearly identical to the real thing.
The difference: a false gate is not deep enough for the sidebar to fully retract. The lock stays closed. In modern Abloy cylinders, the false gates are machined to tolerances within fractions of a millimeter of the true gate — making them essentially indistinguishable from the real thing during manual manipulation. You can "set" every disc in a cylinder and still be completely wrong about whether any of them are actually at the true gate.
Setting a pin tumbler lock feels like a series of satisfying clicks. Setting a disc detainer feels like reaching into fog — every sensation might be real, or it might be a trap your hands walked into.
The Disc Blocking System (DBS): The Kill Switch
Introduced with the Abloy Protec in 2001 and carried forward into Protec2, the DBS is arguably the most significant security feature ever engineered into a mechanical lock. It uses internal return bars that physically link the discs together when under attack.
Here's why that matters: almost all lock picking methodology — across every lock type — depends on manipulating components one at a time. You find the binding pin, set it, find the next, set it. One-by-one manipulation is the universal exploit. The DBS neutralizes it completely. When an unauthorized tool attempts to move an individual disc, the return bars cause the entire disc stack to lock together as a single rigid unit. You can't move disc three without moving all eleven simultaneously. Individual disc manipulation becomes physically impossible.
✓ Why Bump Keys Don't Work
A bump key works by delivering a sharp kinetic impact to the key, which transmits energy upward through the pins, momentarily jumping driver pins above the shear line while the plug is rotated. This relies on the existence of a shear line and spring-loaded pins. Disc detainer locks have neither. There is no shear line to exploit. There are no springs to absorb and redirect kinetic energy. A bump key inserted into a disc detainer lock will simply damage the keyway. The attack vector does not exist.
Anti-Drill Engineering
Physical attack is always the fallback when picking fails. Disc detainer locks address it in layers:
🔩 Anti-Drill Defense Layers
1
Hardened faceplate: A free-spinning, case-hardened steel plate on the cylinder face deflects drill bits. Because it spins freely, a drill bit can't gain purchase — it just rotates the plate without cutting.
2
Free-floating first disc: If a drill penetrates the faceplate, the first disc it encounters is not fixed to any mechanism. It simply rotates with the drill bit, preventing the bit from biting deeper. The drill spins the disc. The disc spins freely. Nothing is cut.
3
Rear-loaded architecture: In many Abloy models, the internal components are loaded from the rear of the cylinder housing. Even if the entire front face is destroyed, the core cannot be pulled forward through the door. You'd need to destroy the door itself.
4
L-shaped sidebar: On high-security models, the L-profile sidebar has a much larger engagement surface than a round one, making it harder to drill around and significantly harder to defeat by any mechanical bypass.
The Anti-Wear System (AWS) and Longevity
The Anti-Wear System, introduced with Protec2, reduces friction between the key bitting and the disc profiles. This matters more than it sounds. A lock that's used 20 times a day in a commercial facility will be cycled over 7,000 times a year. Without wear management, the contact surfaces between the key and discs gradually erode, widening tolerances. Wider tolerances mean the gates become slightly easier to manipulate. AWS reduces this degradation, keeping the lock's security tolerances essentially unchanged over its operational lifetime.
The Interactive Element: Defeating 3D Printing
The Protec2's most forward-thinking security feature is small but decisive: a moving element embedded in the key itself — a spring-loaded ball or "interactive component" — that must physically engage with a specific controller inside the cylinder before the sidebar will drop. A key with the correct bitting profile but without this interactive element won't open the lock. This feature was designed specifically to defeat 3D-printed key blanks and conventionally milled duplicate keys, which can replicate a key's shape but cannot replicate a moving internal component.
Abloy invented the disc detainer lock, but they're not the only game in town anymore. Several manufacturers have developed their own interpretations — some producing direct competitors, others taking the rotational principle in genuinely different directions. Here's how the landscape breaks down.
The Abloy Lineage: A Century of Refinement
ABUS: The German Interpretation
The German manufacturer ABUS uses disc detainer principles in its "Plus" and "X-Plus" cylinders, most notably in the Granit padlock series. A typical ABUS Plus cylinder contains 7 code discs and 2 steering discs. The key difference from Abloy's approach is tensioning location: many ABUS cylinders use middle-tensioning, where the binding disc is in the middle of the stack rather than at the front or rear. This significantly complicates picking attempts, because the traditional approach of starting at one end and working toward the other doesn't apply — you need to identify which disc is the tensioning disc before you can even begin picking.
Anchor Las: Swedish Industrial-Grade
Sweden's Anchor Las makes some of the most physically formidable padlocks on the planet, built to SSF (Swedish security standard) grades that are among the most demanding in Europe. Their disc cylinders typically use 9 discs and a 3mm thick nickel silver key. The Grade 5 models feature 4.5mm thick hardened protection plates and are specifically designed for maritime containers, railway switches, and outdoor infrastructure. If you need a padlock that will still work after years of saltwater exposure and repeated impact attacks, this is the category you're looking at.
Gerda Tytan: 16 Pins, 4 Billion Combinations
The Gerda Tytan ZX from Poland is a fascinating outlier. It's often grouped with disc detainers because of its rotational logic, but it's technically a tubular detainer system — a different architecture entirely. Instead of a stack of discs with a sidebar, it uses 16 pins arranged in four concentric rings (rows A, B, C, D) around a central tubular keyway. The four rows create a permutation count exceeding 4 billion combinations, with tolerances down to 0.02mm — tighter than almost any other mechanical lock in existence.
The Gerda Tytan is famous in Eastern European security and locksport communities as the lock most likely to make experienced pickers give up and go home. It requires a highly specialized decoder tool (the "Gerda Decoder") that is specifically engineered for its 0.02mm tolerances — standard disc detainer tools cannot navigate it.

Let's be straightforward: picking a disc detainer lock is hard. Not "this will take a few hours of practice" hard — "most experienced locksport practitioners still can't reliably open high-security examples" hard. The combination of no spring feedback, false gates, and (in Protec/Protec2) the Disc Blocking System makes this the most technically demanding field in mechanical lock manipulation.
That said, understanding how disc detainer picking works is worthwhile even if you never try it yourself. It illustrates exactly why these locks are so secure — and it informs which locks in the buying guide are actually resistant versus which are just expensive.
First Step: Zeroing the Discs
Before any picking attempt, you need to establish a baseline. Insert the pick tool and rotate all discs as far as they'll go in one direction — this is called "zeroing." You're creating a known starting position so that any disc you subsequently move is moving away from zero in a measurable way. Without zeroing, you're guessing about the starting state of each disc.
Finding the Tensioning Disc
Here's the first critical difference from pin tumbler picking. In a pin tumbler lock, you apply tension to the plug itself. In a disc detainer lock, you apply tension via a specific disc — and finding the right one is half the battle. There are three possible configurations:
🎯 Three Tensioning Strategies
F
Front tensioning: The front-most disc is the driver — rotating it applies torque to the plug. Common in budget padlocks. The easiest to attack because the tensioning disc is predictable.
R
Rear tensioning: The rear-most disc (the "0-cut" position) drives the plug. Common in high-security Abloy locks. Harder to attack because you're reaching past all the other discs to apply tension.
M
Middle/random tensioning: Found in ABUS Plus and Protec series. The tensioning disc is not at either end of the stack. You must identify which disc it is before you can even begin picking the others. Significantly harder — and in modern implementations, deliberately obscured.
The Wobble Test: Hearing What Your Hands Say
Once you've applied tension via the correct disc, the sidebar is being pressed against the disc stack due to the torque you're applying. Here's where physics gets subtle. Because of microscopic manufacturing variances — differences too small to see but real enough to measure — one disc will be pressed against the sidebar harder than its neighbors. That disc is "binding."
You need to find that disc and rotate it until its true gate aligns with the sidebar. The sidebar will partially drop into the gate, and the disc will suddenly feel different: slightly loose, with a small amount of rotational play. This is the wobble test. A set disc wobbles. An unset disc either feels rock-solid (still binding) or hits a hard stop (caught in a false gate, which feels deceptively similar to a true gate).
The wobble is your only honest feedback in a springless mechanism. Everything else — every click, every resistance — might be a false gate lying to your fingertips.
A new binding disc will emerge after each setting. You work through the stack until (theoretically) every disc is set. In practice, with a lock that has false gates, you may think you've set six discs and actually have set two true gates and four false ones — and when you apply more torque to find the seventh, the whole stack moves and you start over.
Decoding: The Professional Level
High-end tools like the Silver Bullet V2 don't just pick the lock — they decode it. By recording the rotational degree at which each disc sets (using the laser-etched graduation marks on the tool), an operator can reconstruct the exact bitting code of the lock. That code can then be used to cut a permanent, working key. This is the capability that makes disc detainer manipulation relevant to government and intelligence applications — covert entry, key duplication, and access with no visible evidence of intrusion.
⚠ Legal Note
Disc detainer picks, like all lock picks, exist in a gray legal area that varies by jurisdiction. In many places, possession is legal but use on locks you don't own is not. This section is provided for educational understanding of security principles. If you want to practice, buy a lock specifically for that purpose and practice on your own property.
You cannot pick a disc detainer lock with standard hooks, rakes, or tension wrenches. The keyway geometry, the internal architecture, and the picking methodology are completely incompatible with pin tumbler tools. Disc detainer picking requires a class of tool built specifically for this mechanism.
The defining characteristic is a 2-in-1 concentric shaft design: an outer shaft that applies tension to the cylinder, and an inner shaft with a tip that reaches individual discs for manipulation. The outer and inner shafts must be independently controllable — you need to hold tension while simultaneously rotating specific discs, which requires both shafts to move independently without transmitting force to each other.
The Three Tiers of Disc Detainer Tools
The Sparrows (LPL/BosnianBill) Pick
This tool was developed through a collaboration between two of locksport's most prominent figures: BosnianBill and the LockPickingLawyer. The intention was a mid-market option that filled the gap between junk Chinese picks and the cost of professional tools. The Sparrows disc detainer pick features a modular tip system and works well on ABUS Plus cylinders and mid-tier locks like Kryptonite. For most enthusiasts who aren't targeting Abloy-level hardware, it's the right tool.
The Silver Bullet V2: What Professional Actually Means
The Silver Bullet V2 is not a consumer product marketed as "professional." It's an actual professional instrument, machined from 17-4 PH stainless steel — an aerospace-grade alloy chosen for its combination of extreme strength, corrosion resistance, and dimensional stability. The tips are under 2.00mm at their narrowest, allowing them to navigate the tight keyways of Abloy Protec and Anchor Las cylinders where other tools physically cannot reach.
It's hot-swappable — different tip configurations can be quickly exchanged for front, rear, or middle tensioning — and it includes laser-etched graduation markings for both depth (disc location within the stack) and rotation (recording gate positions for decoding). This is the tool that intelligence services and professional locksmiths use when they need to get through a high-security disc detainer lock without evidence of entry.

Advertisement · 728 × 90
The disc detainer mechanism has been resistant to electronic replacement for over a century, in part because it doesn't need electronics to be excellent. But the demands of modern infrastructure management — remote access control, audit trails, key revocation — have pushed even Abloy toward hybrid systems.
The PROTEC2 CLIQ is the current answer. It combines the full mechanical security of the Protec2 disc cylinder with an encrypted electronic chip embedded in the key. The system is powered by a battery inside the key itself — no external wiring, no door electronics, no network dependency at the point of entry. When the key is inserted, the chip communicates with a receiver in the cylinder. If the electronic authorization is valid and the mechanical bitting is correct, the lock opens. Either factor alone is insufficient.
✓ What CLIQ Enables That Pure Mechanical Cannot
- Time-based access: A key can be programmed to work only between 8AM and 6PM, or only on weekdays, or only for a specific 24-hour window.
- Remote revocation: A lost or stolen key can be electronically invalidated. Even if the mechanical bitting matches, the electronic authorization is gone.
- Audit trails: Both the key and the cylinder record every opening event — timestamp, key ID, location. Indisputable access records for security investigations or compliance.
The broader implication is significant: as mechanical patents expire (Protec2's patent runs until 2031), the electronic layer provides a continuously evolving secondary barrier. You can copy the mechanical bitting once it's in the public domain. You cannot replicate an encrypted authentication chip. The disc detainer's future — like its past — is about staying one step ahead of the attacker.
Buying Guide
Which One Should You Actually Buy?
Recommendations from the enthusiast community and our own testing — organized by budget and use case. All affiliate links use our Amazon tag; purchasing through them supports NoPryZone at no cost to you.
Zarker
J45 / J45S
The community's unanimous "first disc detainer" recommendation. Affordable and has unusually crisp tactile feedback for its price point — which matters enormously when you're learning to feel the difference between a true gate and a false one. The J45S is the shackle-protected variant.
Beginner Friendly
Front Tension
Locksport Starter
View on Amazon →
Affiliate link · supports NoPryZone
Yale
Y112
A solid budget padlock commonly used in locksport's "Orange Belt" challenges. Represents a genuine step up in build quality from generic Chinese locks while remaining accessible. Often recommended as the second disc detainer purchase after the Zarker.
Orange Belt
Good Build Quality
View on Amazon →
Affiliate link · supports NoPryZone
FJM Security
SX-795-KD
A hardened steel D-shaped padlock commonly used on storage units. The D-shape protects the shackle from bolt cutter attacks. Smooth disc mechanism is manageable for beginners while offering more physical security than most budget padlocks.
Hardened Shackle
Storage Use
View on Amazon →
Affiliate link · supports NoPryZone
Kryptonite
KryptoLok Series
The most common disc detainer lock in North America, primarily known for bicycle security. Considered high-tier for the price point, balancing portability with a genuinely pick-resistant disc cylinder. If you're locking a bike in a city, this is a well-proven choice.
Best Value
Bike Security
North America Standard
View on Amazon →
Affiliate link · supports NoPryZone
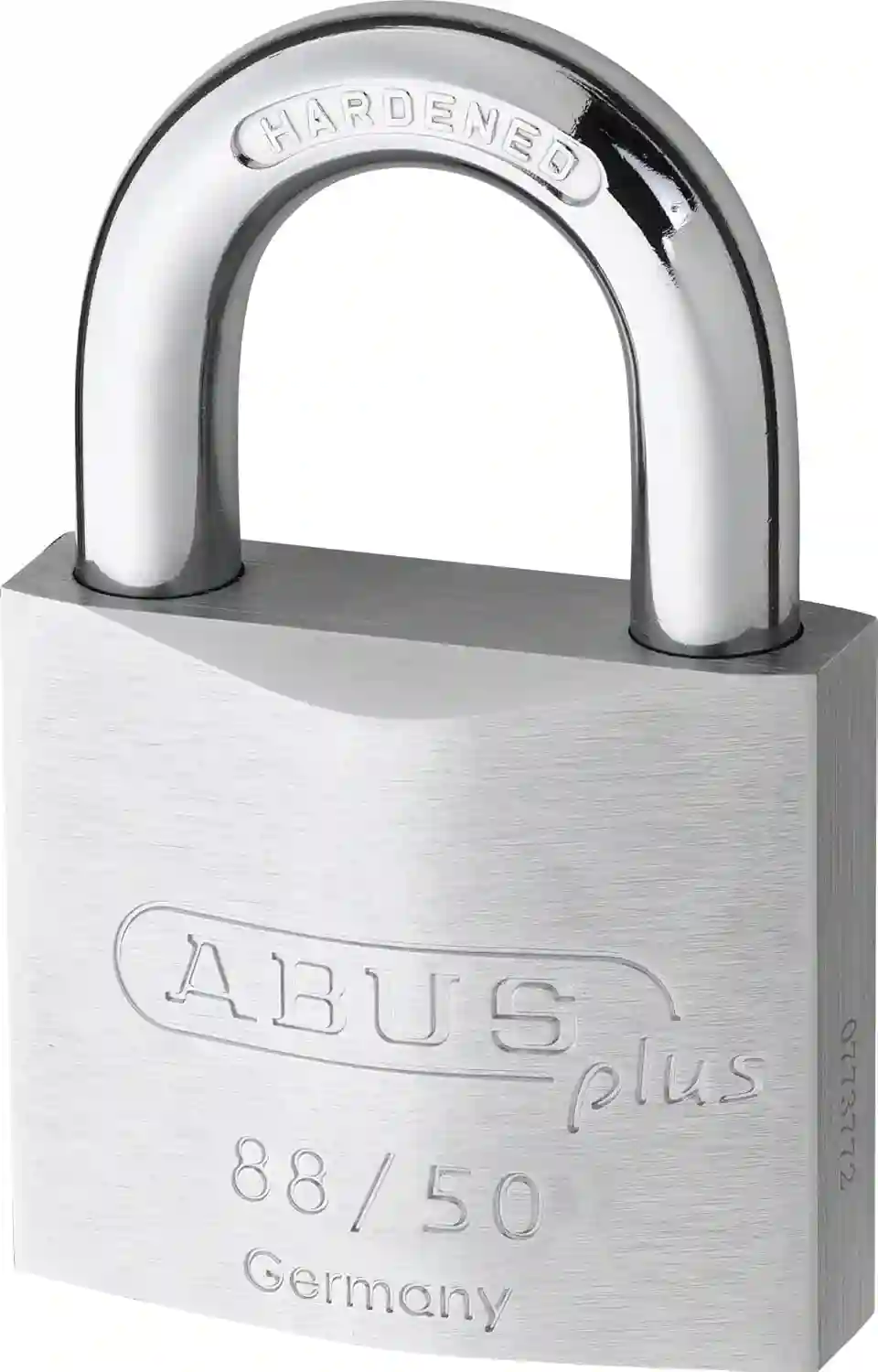
ABUS
Plus 88/50
A classic German-engineered padlock with a 7-disc "Plus" cylinder and precision false gates. The middle-tensioning design makes it significantly harder to pick than front-tension alternatives. Widely respected for precise manufacturing tolerances and consistent durability over time.
7 Code Discs
Middle Tension
German Made
View on Amazon →
Affiliate link · supports NoPryZone
Anchor Las
820-2 (SSF Grade 3)
Swedish-made brass padlock using a rotating disc system similar to Abloy. More accessible than their maximum-security models but significantly more secure than any pin-tumbler alternative in this price range. SSF Grade 2 rated — a Swedish standard that's meaningfully harder to achieve than its number suggests.
Swedish Made
SSF Grade 2
9 Discs
View on Amazon →
Affiliate link · supports NoPryZone
Abloy (ASSA ABLOY)
Protec2 PL330 / PL362
The global benchmark. 11 discs, 1.9 billion combinations, Disc Blocking System, Anti-Wear System, interactive key element that defeats 3D-printed blanks. Patent-protected until 2031. Rated for extreme environments. Used by telecom, power, and government infrastructure worldwide. The PL362 has a shackle guard for exposed applications.
Global Benchmark
1.9B Combinations
DBS Equipped
Patent 2031
View on Amazon →
Affiliate link · supports NoPryZone
ABUS
Granit 37/80
Routinely cited as one of the toughest padlocks in the world. Shrouded shackle is essentially bolt-cutter-proof, and the disc tumbler cylinder is bump-proof by design. The combination of physical hardening and disc security makes this one of very few locks that resists both covert and overt attack methods at a high level.
Shrouded Shackle
Bump Proof
German Made
View on Amazon →
Affiliate link · supports NoPryZone
Anchor Las
880-4 (SSF Grade 4/5)
Heavy-duty industrial Swedish lock built for maritime containers and critical infrastructure. 15mm hardened steel shackle. 3mm thick free-spinning anti-drill protection plate on the cylinder face. Designed to survive torque attacks, liquid nitrogen, and saltwater corrosion. This is the lock on shipping containers crossing the ocean.
SSF Grade 4/5
15mm Shackle
Maritime Rated
Anti-Drill Plate
View on Amazon →
Affiliate link · supports NoPryZone
Gerda (Poland)
Tytan ZX
A legendary surface-mounted door lock from Poland that operates on a complex rotational detainer principle with 16 pins across four concentric rows and over 4 billion combinations. Tolerances down to 0.02mm. Requires a purpose-built decoder tool that costs more than most padlocks. Considered virtually unpickable without it. A high-level locksport trophy and a genuinely excellent security product.
4B+ Combinations
16-Pin Tubular
0.02mm Tolerances
Locksport Trophy
View on Amazon →
Affiliate link · supports NoPryZone
The Bottom Line
What 117 Years of Lock Design Teaches You
Emil Henriksson's insight in 1907 wasn't about security — it was about geometry. The disc detainer lock works because it replaced a linear, spring-dependent system with a rotational, springless one, and that single architectural decision made an entire category of attacks physically impossible.
For most people, the practical takeaway is simple: if you need a padlock that resists picking, bumping, and harsh environmental conditions, any disc detainer lock is a significant upgrade over pin tumbler alternatives at the same price. The Zarker J45 at $25 is already more pick-resistant than most $80 pin-tumbler padlocks. The Abloy Protec2 at $150+ is the closest thing to an unpickable mechanical lock that consumer money can buy.
For locksport enthusiasts, disc detainers are the summit of the mountain. The wobble feedback, the false gates, the DBS — this is the category where technical skill and high-quality tools are both required, and where "I opened it" is a genuine achievement rather than an afternoon of practice.
For security professionals and infrastructure managers: Abloy Protec2 and Anchor Las Grade 4/5 are the benchmarks your specifications should reference. Not because nothing else exists, but because nothing else has been attacked this thoroughly, this long, by this many people — and is still standing.